Platform Architecture
The First Watch® platform is purpose-built for Active Protection of industrial control systems. It stops unauthorised project files, unauthorised firmware changes, and incorrect setpoints from being sent to PLCs — preventing the impact of an attack before it starts.
The foundational principle of the system is:
Everything which is not explicitly allowed is forbidden.
The First Watch platform implements a Zero-Trust Architecture for operational technology environments.
What the Platform Does
To achieve active protection, the platform:
- Detects all communication points and identifies industrial assets (users, hardware such as HMI and PLC, software), profiles their baselines, and maintains control over their integrity
- Hardens security configurations of assets to reduce their attack surface
- Learns how assets should normally behave
- Creates end-to-end policies to explicitly allow only processes and actions that conform to permitted operations
- Raises alarms if a policy has been violated, and notifies the asset owner via email/SMS
- Stops the action from being completed
- Facilitates change management and establishes control over changes, preventing unauthorised ones
- Provides a security layer via a mesh VPN network to secure connections to the PLC
Data Collection and Authentication
To implement authentication and authorisation mechanisms in the OT environment, First Watch gathers a near real-time, time-ordered cyber event data stream on each subject and object of every industrial business transaction across the network, including:
- Users — who is performing the action
- Source and destination devices — computers, engineering stations, HMIs, controllers, sensors
- Software and processes — the engineering application in use (e.g. Studio 5000 for ControlLogix)
- Communication channels — protocols and ports
- Intermediate devices — switches, firewalls, gateways
- Content — what is being transmitted
- Type of engineering operation — programming PLC, updating firmware, modifying settings — identified through Deep Packet Inspection (DPI)
- Timestamp — synchronised across machines and devices
This data is stored in a real-time database with synchronised timestamps from the different machines and devices.
Platform Components
The platform is delivered with three core components:
ControlGuard
ControlGuard is a coordinated set of Windows kernel drivers installed on SCADA/HMI machines.
Malicious activities and unauthorised access can originate from any computer on the internal OT network, requiring monitoring of all possible blind spots. ControlGuard provides continuous, comprehensive, real-time visibility into what is happening on endpoints — HMI machines, engineering stations, historians, Active Directory servers, and other critical systems.
ControlGuard detects actions including:
- Launching unauthorised processes
- USB device connections
- Installation of new software
- Changes in IP addresses
- Traffic destinations and payload content
All activities are attributed to the user. All objects and actions must be whitelisted — otherwise, they are not authorised to carry out any action.
The digitally signed kernel driver, verified by Microsoft, is the core component of ControlGuard. Operating at the kernel level, ControlGuard protects industrial computers from cyber-attacks and makes the system considerably more secure against attackers who prefer to work in user space — a level above the operating system.
ControlGuard can effectively shut down ransomware because it is typically bespoke software and therefore not authorised to run. A cyber intruder with compromised administrator credentials cannot stop ControlGuard if it is configured for Protected Mode.
Installation is straightforward and does not require significant downtime. Immediately after deployment, ControlGuard provides information about the endpoint's configuration, begins monitoring the operator's actions, and reports them to the First Watch Controller.
PLCGuard
PLCGuard is a deep-packet inspection and network flow monitoring and filtering engine that observes industrial control network activity and drops packets based on policy.
This technology was purposely built for the unique characteristics of industrial control systems. PLCGuard is specifically designed to detect control layer events in SCADA communications by analysing protocols such as CIP, DNP3, Modbus, and S7CommPlus.
PLCGuard capabilities include:
- Real-time visibility — In-depth, real-time visibility into all activities performed over the operational network, including code downloads/uploads, firmware changes, PLC setting modifications, hardware configuration changes, and tag read/write commands. Industrial security engineers and asset owners receive detailed, real-time alarms and can mitigate security events before damage occurs.
- Forensic event log — A comprehensive event log that can be used for forensic investigations.
- Protocol monitoring and filtering — Monitors or filters traffic flows and recognises modern network protocols such as DNS, SSH, HTTP/S. The operational team can immediately detect unauthorised communications or usage of unknown and unauthorised network protocols (e.g. disallowed connection of an industrial device from a host connected to the Internet).
- Asset discovery — PLCGuard natively discovers all devices on the OT network, including PLCs, and provides essential information about device attributes: vendor, controller model, installed firmware version, serial number, product codes, and more.
- Industrial firewall — PLCGuard can be configured as an industrial firewall inspecting industrial network traffic with DPI (Deep Packet Inspection), stopping unauthorised actions including code downloads/uploads, firmware changes, PLC setting modifications, hardware configuration changes, and tag read/write commands.
- Mesh VPN — PLCGuard serves as the foundation for a distributed, secure mesh VPN, providing an additional security layer.
Controller
The First Watch Controller is the central server for centralised management of gathered data and centralised policy management.
The Controller collects and processes events from PLCGuards and ControlGuards, generates alarms, and visualises the organisation's cybersecurity posture. It is the daily instrument for the asset owner, automation engineer, or security analyst to observe the situation in the OT network and immediately react to suspicious behavioural actions in the environment — whether malware or human-generated.
Based on gathered data, an engineer can produce all necessary policies to control the industrial perimeter. Policies are distributed to the ControlGuards and PLCGuards.
Active Protection Model
Active Protection is based on a set of rules (policies) created within the First Watch platform to protect a specific aspect of an industrial environment.
Policies are stored and maintained on the ControlGuards to protect HMI computers and on the PLCGuards to protect the PLCs. Once deployed, ControlGuards and PLCGuards check gathered events against policies and stop any action that violates the policy.
A unique feature of the First Watch platform is its resilience if the administrator's password is compromised — ControlGuard's Protected Mode prevents an attacker from disabling protection even with elevated credentials.
High-Level Architecture
The First Watch® platform has a secure and modular containerised architecture. This provides flexibility and scalability to meet the varied requirements of different OT networks. It can be deployed in cloud, on-premises, or hybrid configurations, and allows secure updates of functional blocks on-the-fly.
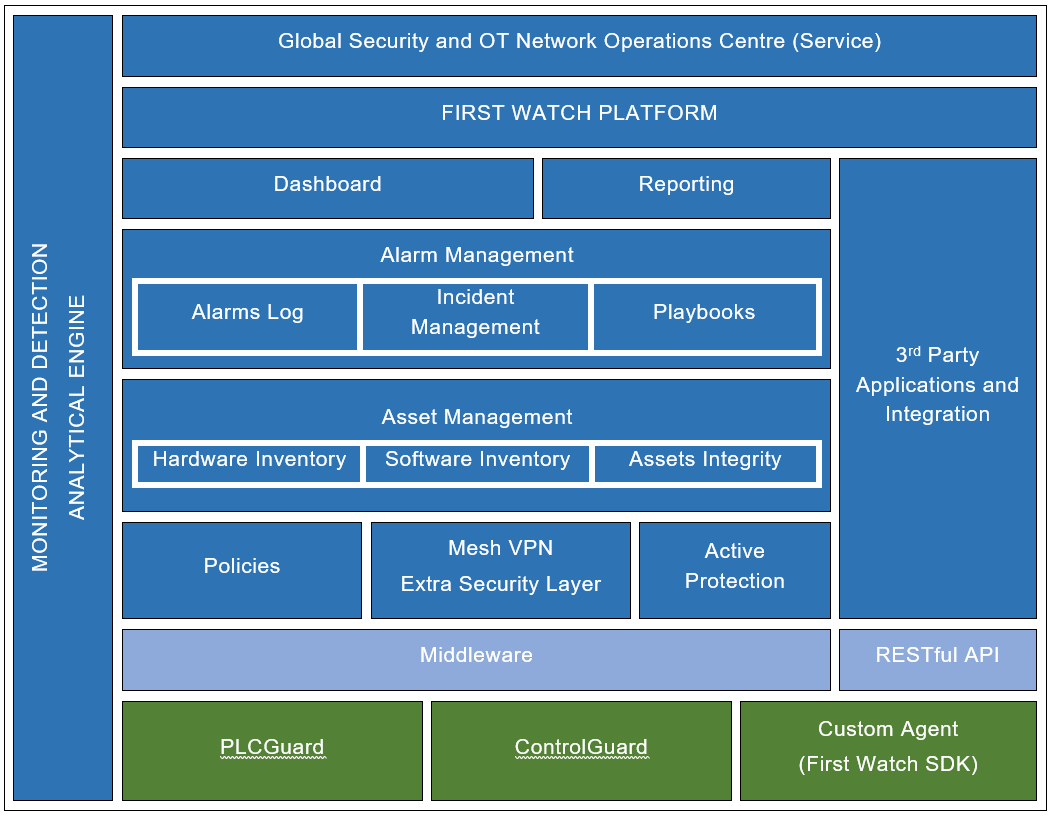
The platform architecture comprises:
| Layer | Capabilities |
|---|---|
| Monitoring and Detection | Analytical engine, global security and OT network operations centre (service) |
| Dashboard | Reporting, third-party application integration |
| Alarm Management | Alarms log, incident management, playbooks |
| Asset Management | Hardware inventory, software inventory, asset integrity |
| Policies | Mesh VPN, extra security layer, active protection |
| Middleware | RESTful API |
| Edge Components | PLCGuard, ControlGuard |
Additionally, the First Watch engineering team can offer a monitoring service to customers, providing a 24/7 specialist response capability.
Core Technologies
The First Watch® platform is based on proprietary, patented technology developed by the University of Waikato. The patent application is filed in the USA, Europe, China, India, and Australia.
Each core technology focuses on different and unique aspects of control layer activities, solving OT challenges. These innovative technologies provide unmatched visibility into OT activities — especially control layer events that impact critical controller logic — and the opportunity to actively protect HMIs and PLCs from unauthorised action.
Deployment Topology
The platform supports flexible deployment topologies:
- Single-site — All components deployed within one facility
- Multi-site — Multiple sites managed from a single Controller instance
- Distributed — Multiple Controller instances for geographically separated or air-gapped environments
The containerised architecture allows deployment in cloud, on-premises, or hybrid configurations depending on site requirements and connectivity constraints.
Offline Resilience
Enforcement decisions are made at the edge — on the workstation (ControlGuard) and on the network (PLCGuard) — not in the cloud. The platform continues enforcing policy locally even when the Controller is unreachable.
Policies are stored and maintained locally on ControlGuards and PLCGuards, ensuring continuous protection regardless of network connectivity to the central Controller.