Core Capabilities
The First Watch® platform delivers a comprehensive set of core capabilities designed to address the operational, security, and compliance requirements of industrial control system environments.
| Capability | Purpose |
|---|---|
| Asset Visibility & Inventory | Real-time, accurate tracking of all OT/IT assets to build a trusted baseline and enhance governance without operational disruption |
| Change Detection & Provenance | Record all changes for accountability and audits, enabling up to 52% faster incident resolution through evidence-based insights |
| Endpoint Protection (ControlGuard™) | Secure critical SCADA and engineering workstations and servers with policy-driven controls that reduce unauthorised risks while maintaining industrial stability |
| Network Monitoring & Protection (PLC Guard™) | Visibility into industrial PLC communications with enforced zoning to minimise vulnerabilities and attack surfaces |
| Policy Governance & Control | Centralised security policies with audit trails and managed exceptions for maintenance, ensuring controlled and compliant operations |
| Reporting & Compliance Support | Defensible, data-driven reports for seamless audits, regulatory compliance, and executive oversight |
| Data Export & Integration | Seamless integration with enterprise systems for comprehensive risk management and workflow optimisation |
| Operational Risk Reduction | Reduced investigation time, audit preparation effort, and contractor-related incidents through defensible, time-aligned evidence of system behaviour and changes |
| Stateful Alarm Management | Fully configurable, stateful alarms with lifecycle tracking — notifications delivered to mobile and email for immediate response |
| Custom Agents (First Watch SDK) | Build custom-made agents using the First Watch SDK to extend platform capabilities for site-specific monitoring and control requirements |
Deterministic Policy-Driven Control
The First Watch® platform is designed around a deterministic, policy-driven control model consistent with industrial engineering principles. It does not introduce heuristic or unpredictable behaviour into control environments. Instead:
- All monitoring and enforcement actions are defined by explicit policies
- Behaviour is evaluated against approved rules and operational context
- Enforcement decisions are predictable, auditable, and repeatable
The platform complements existing control and safety systems — PLC logic, interlocks, SIS, firewalls — without modifying control algorithms or affecting scan-cycle determinism. It operates alongside the control architecture, providing visibility and governance while preserving:
- Deterministic process behaviour — no interference with control loop timing or execution
- Approved maintenance workflows — existing procedures continue to function under policy
- Engineering authority over change — the platform enforces what engineers define
Progressive adoption is supported: organisations can move from visibility to monitoring and then to active protection only after operational baselines are validated and approved. Security controls are introduced in a controlled and predictable manner — aligned with maintenance windows, engineering approvals, and process constraints.
By embedding deterministic policy enforcement, scoped application, and fail-safe mechanisms, the platform strengthens cybersecurity governance without compromising operational stability or engineering discipline.
Asset-Centric Operations
Within the platform, an asset is any entity that communicates, executes logic, or influences the industrial process. This includes, but is not limited to:
- Communicating devices — PLCs, RTUs, IEDs, HMIs, SCADA servers, switches, and gateways
- Software assets — firmware, operating systems, control applications, and engineering tools
- Engineering and operational software — programming environments, diagnostic utilities, and vendor tools
- User and system accounts — accounts with access to industrial systems
Treating all of these elements as assets ensures that operational awareness extends beyond hardware alone and reflects the true cyber-physical system.
Policy-Driven Operational Control
All operational activities within the platform are governed by flexible system policies. These policies translate operational intent into enforceable rules that define acceptable behaviour.
Policies are used to specify:
- Which assets must be monitored
- What types of changes must be detected and recorded
- What types of changes must be restricted or prevented
- Under which conditions exceptions are permitted
This approach allows organisations to adapt controls to their operational maturity, risk tolerance, and process criticality.
Detection Versus Prevention
Not all changes require prevention. In industrial environments, it is often safer to detect and review changes that are expected or low-risk, and prevent changes that are unauthorised, unsafe, or outside approved conditions.
Policies therefore distinguish between:
- Observable changes — logged and reviewed for accountability
- Prohibited changes — actively blocked unless explicitly authorised
This distinction enables disciplined governance without unnecessarily constraining legitimate operations.
Objectives in Practice
Together, these capabilities enable the platform to:
- Maintain continuous visibility of assets and their interactions
- Ensure that changes are intentional, authorised, and traceable
- Support safe evolution of industrial systems
- Provide evidence-based oversight for operations, security, and compliance
By combining asset-centric visibility with policy-driven control, the First Watch® platform supports operational objectives while respecting the realities of industrial environments.
Technical Capabilities
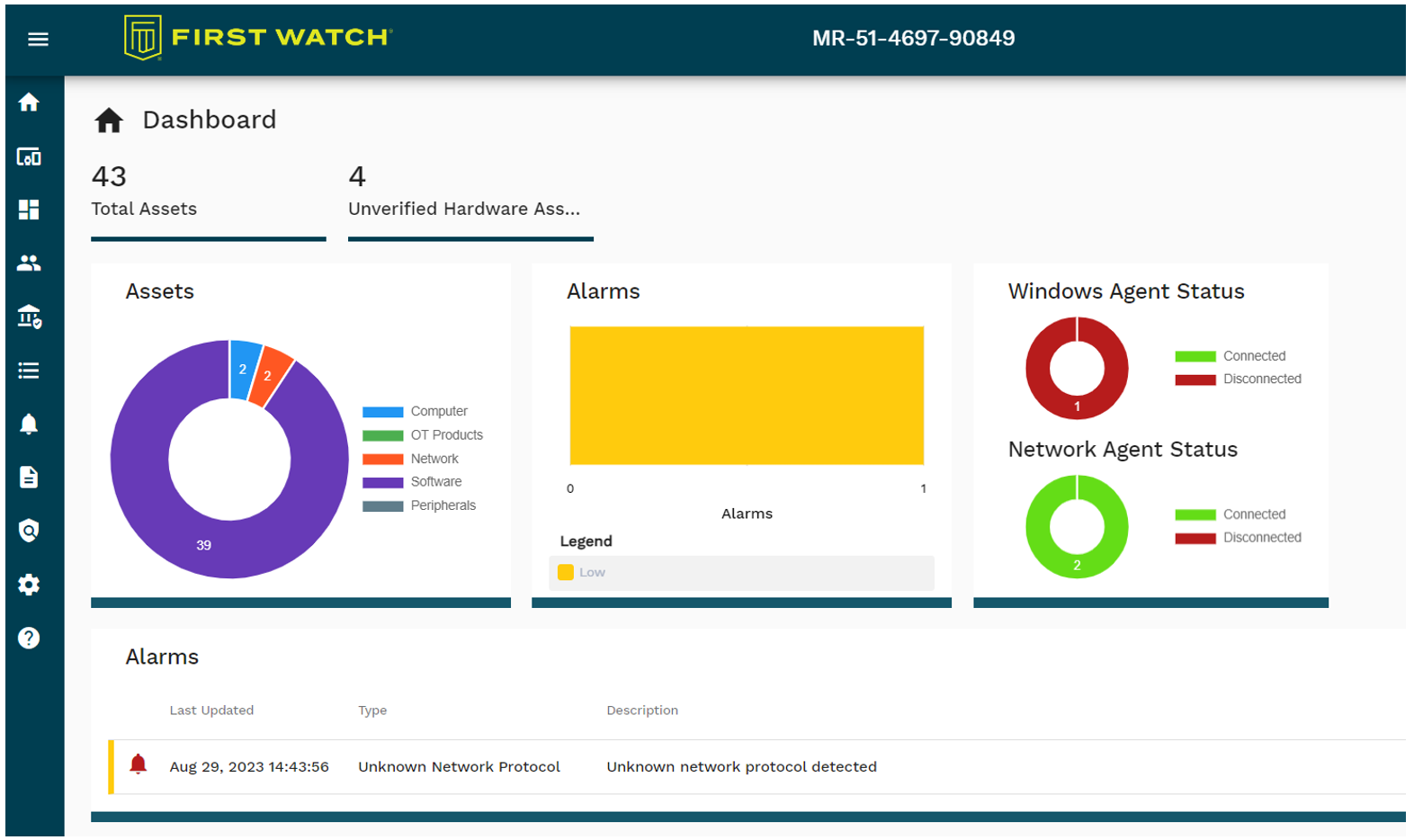
Dashboard
The dashboard provides summary views and detailed reports to support the implementation of security best practices. It includes a real-time alarms view interface, giving operators and security analysts an operational cybersecurity snapshot at a glance.
Reporting
The platform includes a set of predefined reports that give detailed insight into the cybersecurity posture of the OT network. Reports cover assets, asset changes, vulnerabilities, generated alarms and their status, communications, and recently connected devices. All reports are CSV-formatted and can be downloaded for further analysis.
Policies
The granular rule-based system enables security professionals to establish security and change management policies, allowing them to receive real-time alarms on unauthorised activities or actively shut down malicious actions.
Examples of policies:
| Policy | Description |
|---|---|
| 1 | Allow User_1 to use SCADA software to communicate with PLC_1 using only CIP protocol and read the process variable |
| 2 | Allow User_2 to use Engineering software to communicate to PLC_2 by using only Modbus protocol, read and write to PLC except for firmware upgrade |
| 3 | Allow User_3 to use Engineering Software to upgrade the firmware on PLC_2 only on the 1st day of every month and disallow it on any other day |
| 4 | Block unauthorised USB removable media |
| 5 | Allow only authorised applications |
The policy management mechanism is a flexible engine that allows configuration of what must be detected and what must be stopped. Templates, alarms, and notification recipients can be configured. Policies can be written for an individual agent or a group of agents.
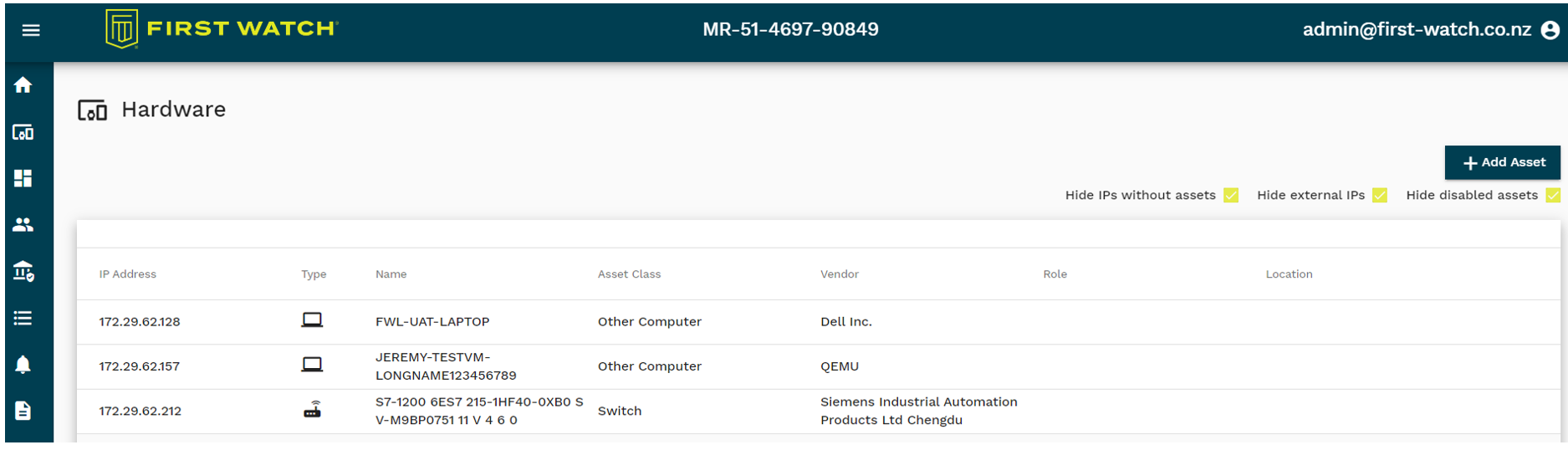
Asset Management
Hardware Inventory
PLCGuard and ControlGuard provide automated discovery of all devices connected to the OT network, including PLCs. The comprehensive, up-to-date inventory includes details such as the manufacturer, controller model, firmware version, serial number, and product codes. The inventory updates as new assets appear on the network and older assets are removed or replaced.
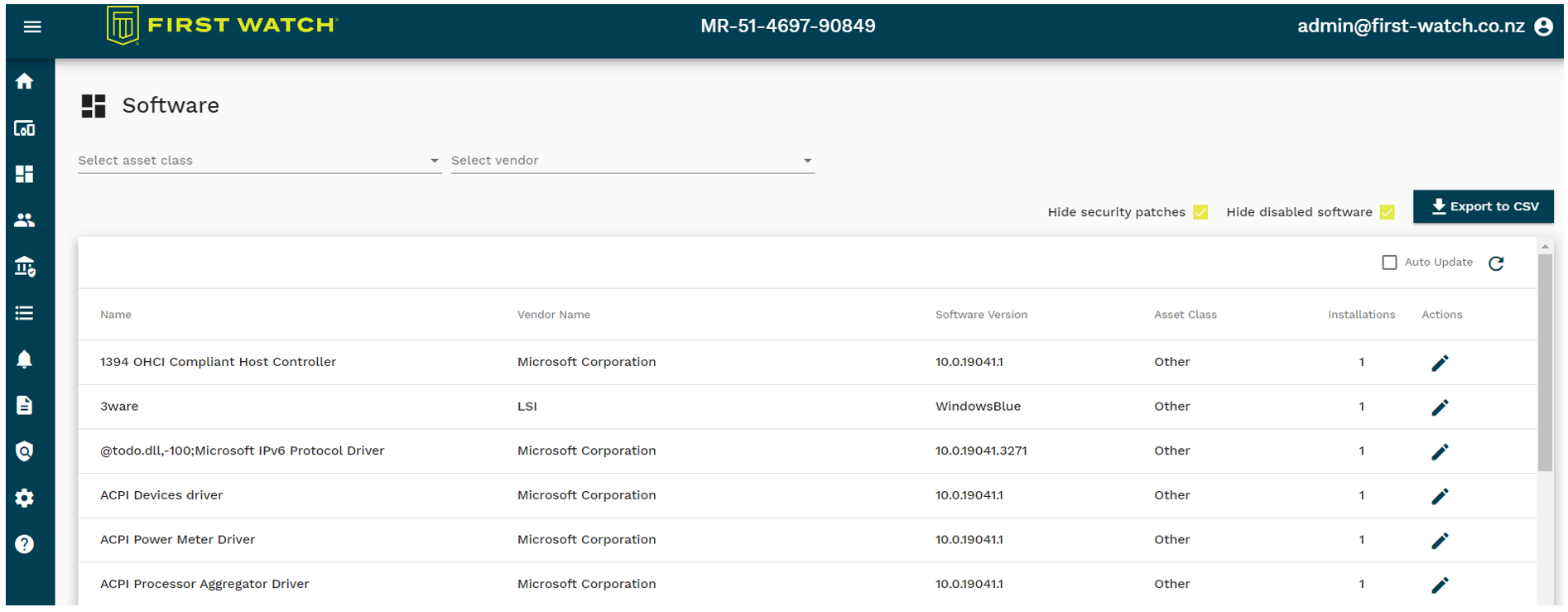
Software Inventory
ControlGuard provides automated discovery of all software packages installed on HMI machines connected to the OT network — including legitimate software, system components, drivers, services, and containerised software. The inventory includes the manufacturer, software name, version, installed path, and other relevant details. It updates as new software appears on the endpoint, and older assets are removed or replaced. An industrial device's firmware is treated as a software asset.
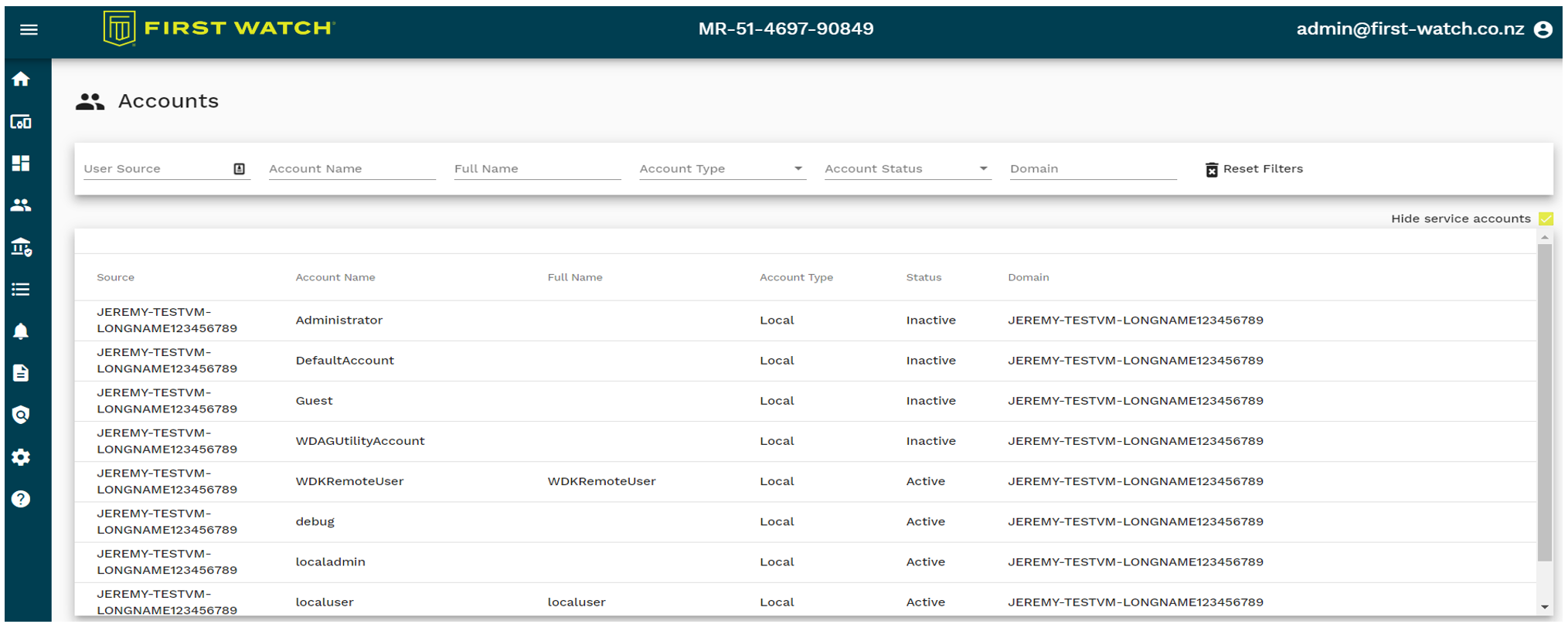
Users
The platform constantly detects information from various sources and presents accounts along with their attributes. These accounts can be used in policies to either restrict access or grant specific rights.
Asset Integrity Control
The platform tracks and logs all changes to the integrity of assets. First Watch®'s core technologies capture all changes — whether executed by a human, by malware over the network, or physically on a device.
Examples of events collected by the platform and reported to the asset owner:
- Deactivation of an antivirus on an HMI computer
- Firmware update on a PLC
- Replacement of a DLL file (tampered software is not allowed to run)
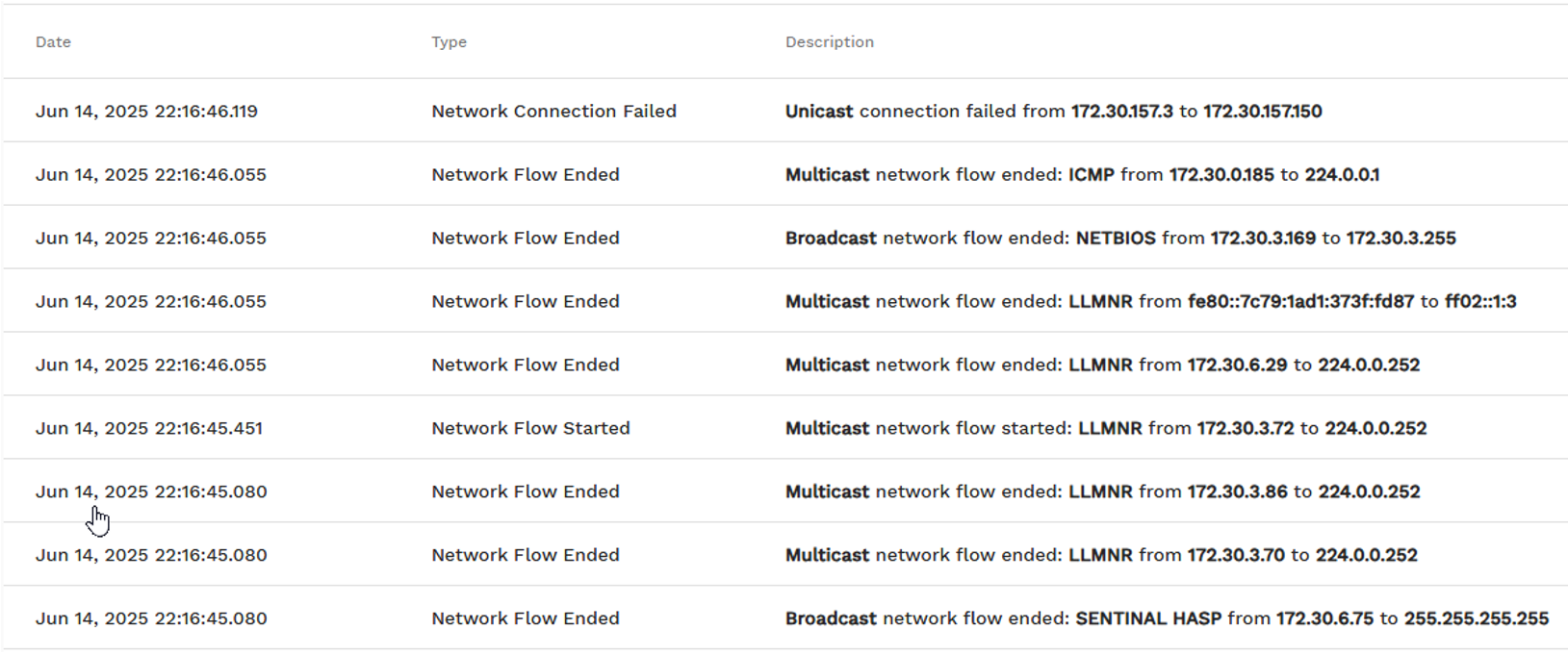
Alarm Management
Incident Management
The platform monitors all critical events — authorised or unauthorised — in an OT environment. Events requiring a user to respond are classified as alarms to be resolved by the appropriate team member. Alarms are completely configurable.
Examples of alarms:
- A new device is connected to the network
- Asset configuration is changed
- A new vulnerability is detected
- An IP address has been changed
- An HMI computer is disconnected
- A firmware update attempt is detected
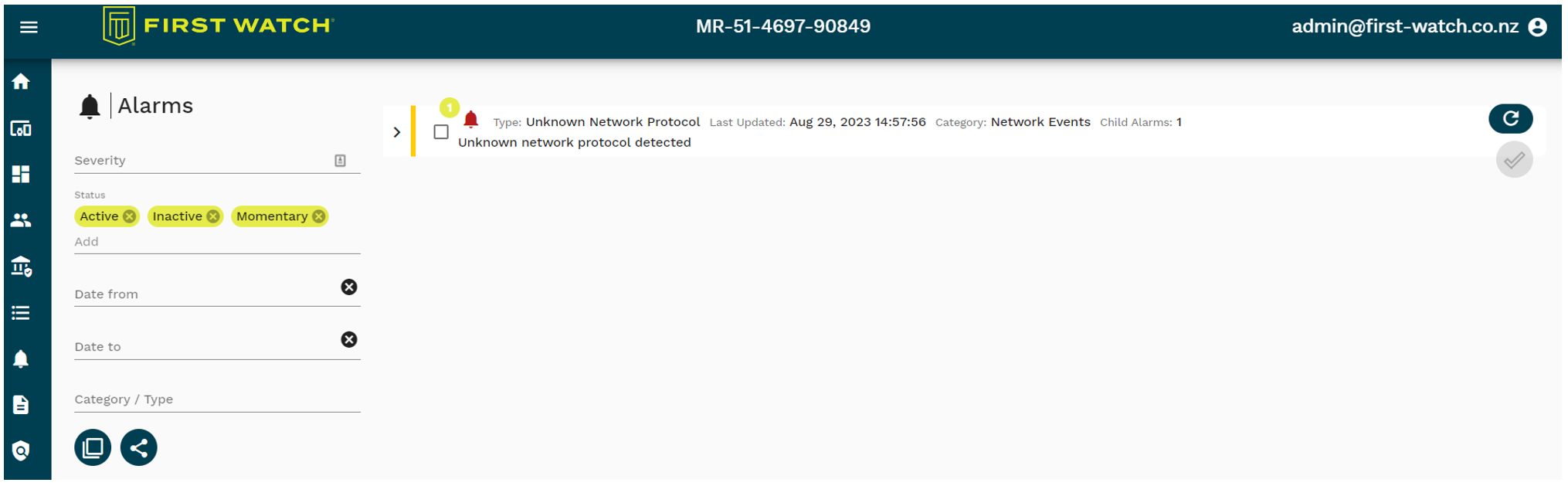
Notifications can be sent to the responsible person via email, TXT, or SMS with details of the raised alarm. Alarms are configurable and based on the data gathered by the platform.
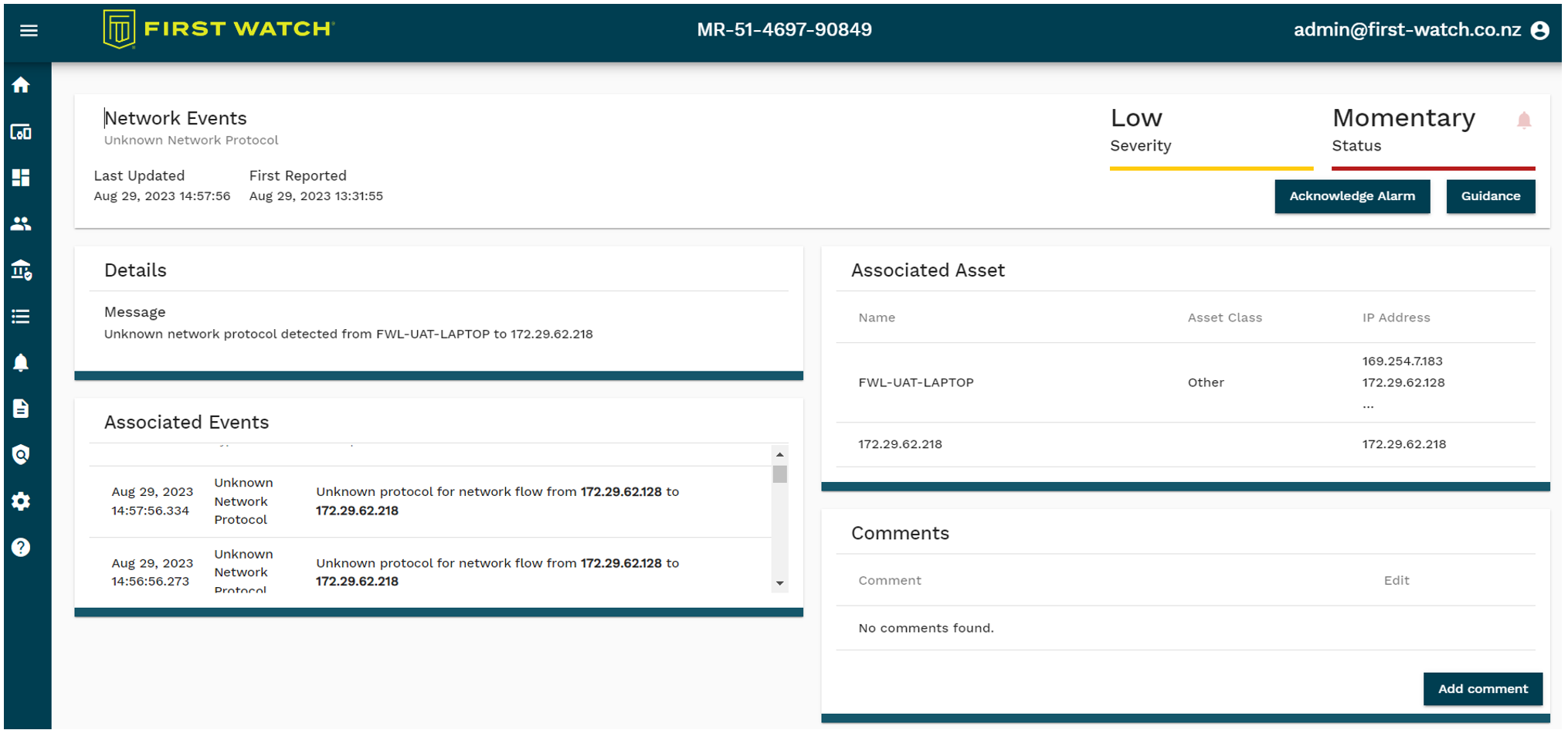
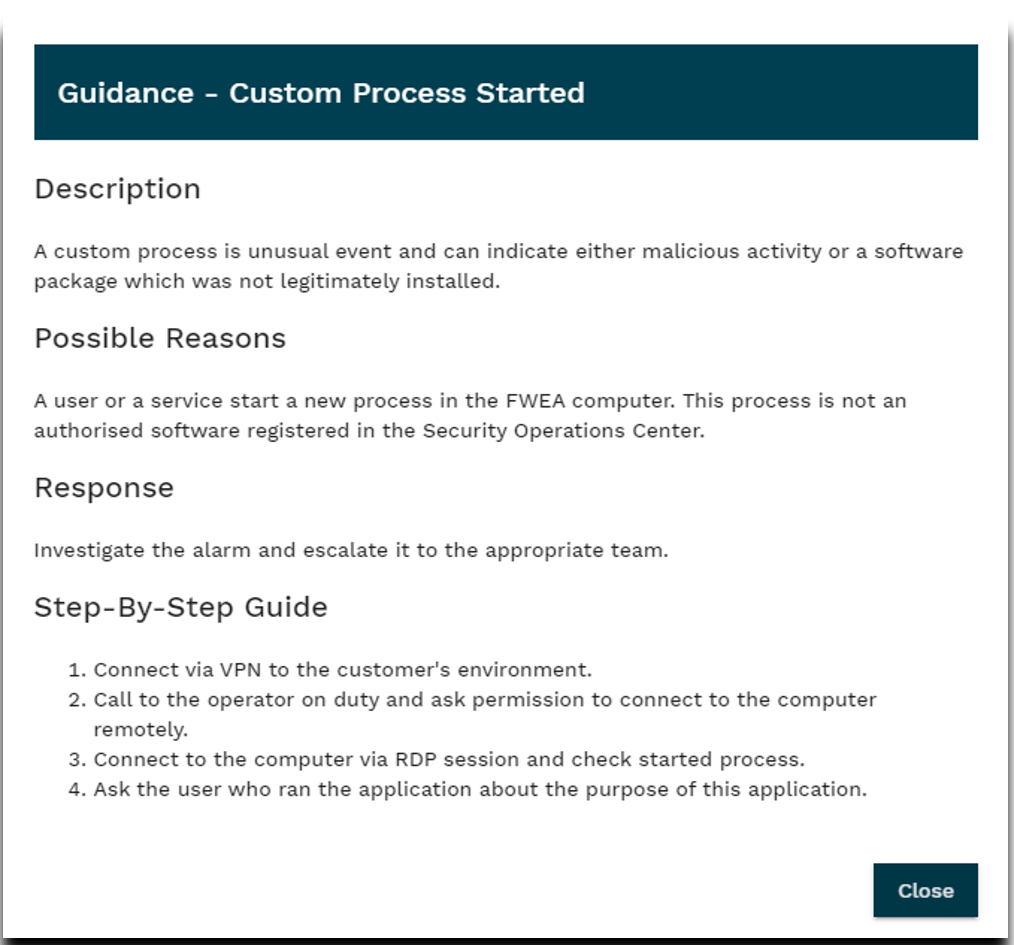
Playbooks
Playbooks provide step-by-step instructions explaining what needs to be done to resolve each type of alarm. They help operators and security analysts reduce the time required to react to cyber incidents. A quick response is beneficial in minimising potential damage when an incident does not commonly occur. Playbooks are configurable.
Mesh VPN (Extra Security Layer)
A PLC connected to an IP network is immediately a target for malicious attackers — devices are visible over network layers and can be explored and exploited. A mesh VPN layer where all critical OT asset components are connected makes PLCs invisible to attackers.
The Security Layer brings essential Zero-Trust Architecture features: authentication and authorisation. Users must be explicitly allowed to connect to the Security Layer before they can see field devices.
Third-Party Applications and Integration
The First Watch® platform supports external integration through RESTful API. Streamlined integration allows clients to maximise their return on investment. Integration can work in both directions:
- Outbound — sending data to an external system (e.g., SIEM, CMDB)
- Inbound — collecting data from an external system (e.g., logs from devices or applications)