Cybersecurity for Solar Farm

Solar Farm as Critical Infrastructure
Solar farms provide a reliable source of electrical power, particularly in regions with favourable climatic conditions. At an industrial scale, these facilities occupy extensive land areas and are typically situated on low-cost terrain, often in remote locations with limited infrastructure. Such settings can present operational challenges, including unreliable Internet connectivity and significant distances from urban centres or technical support.
Despite their isolation, solar farms form an integral part of national critical infrastructure. Through their direct connection to the national grid, they play a crucial role in maintaining energy stability and supply continuity. Any disruption — whether through system failure or cyber intrusion — has the potential to cause cascading power outages or damage to key assets such as inverters and transformers, with widespread operational and economic consequences.
Customer Profile
- Multiple solar farms connected to the National Grid
- Single automation engineer and no IT/Cyber team on-site
- Remote location with unreliable Internet connection
- Limited local technical resources, increasing operational and cybersecurity risk exposure
Solar Farm Process and Key Challenges
Modern solar farms, as integral components of national critical infrastructure, depend on complex ecosystems of SCADA systems, PLCs, inverters, sensors, and communication gateways to manage energy generation and grid synchronisation.
Their high degree of interconnectivity — spanning local controllers, remote substations, and grid telemetry systems — creates multiple operational and cybersecurity challenges that demand robust protection.
Limited On-Site Technical Expertise
Challenge: Solar farms operate with minimal staff and no dedicated cybersecurity expertise, creating delays in detecting and responding to incidents.
Malicious Outcome: Attackers can exploit this gap to gain persistent access, manipulate PLC logic, or disable protection mechanisms.
First Watch Solution: First Watch continuously monitors SCADA traffic and control logic, identifying abnormal data flows and unauthorised code execution. When a threat is detected, the system immediately blocks malicious payloads and quarantines compromised devices, stopping lateral movement before damage occurs.
Unreliable Internet Network Connectivity
Challenge: Remote solar farms often operate with unstable Internet connections, creating monitoring gaps where threats can execute unnoticed.
Malicious Outcome: During communication outages, malware can activate internally, propagate across PLCs, or alter configurations without detection.
First Watch Solution: First Watch operates in offline detection mode, continuously analysing internal traffic and device activity even without Internet access. It captures and drops malicious packets locally, and once connectivity resumes, it synchronises full forensic data and ensures all detected threats are neutralised or blocked from re-entry.
Remote Access and Vendor Dependency
Challenge: Third-party vendors often perform maintenance remotely, sometimes through unsecured or shared credentials, increasing exposure to malicious uploads.
Malicious Outcome: A compromised vendor session could deliver malware disguised as an application update or configuration file, infecting SCADA and engineering systems.
First Watch Solution: First Watch monitors all inbound remote traffic in real time, validating file integrity and protocol behaviour. It detects and blocks suspicious uploads to SCADA or command sequences, halts unauthorised data transfers, and alarms operators to potential malware delivery attempts over remote sessions.
Lack of Real-Time Visibility and Protection
Challenge: Solar farm control networks often lack continuous visibility and active defence mechanisms. Security audits are performed periodically, leaving long intervals during which malicious activity can occur unnoticed. Without real-time protection, operators remain blind to emerging threats until significant disruption has already taken place.
Malicious Outcome: During these visibility gaps, malware can infiltrate SCADA or PLC systems, quietly mapping the network, harvesting credentials, or modifying control logic. Such hidden activity can escalate into coordinated shutdowns, inverter failures, or data corruption before any alarm is raised.
First Watch Solution: First Watch establishes real-time visibility and protection across all SCADA and OT communications. Its continuous deep-packet inspection and behavioural analysis detect command anomalies and unauthorised code changes as they occur. The system immediately blocks malicious sessions, isolates compromised assets, and restores safe operational states, ensuring that no threat remains hidden or uncontained within the control environment.
Integration with National Grid Infrastructure
Challenge: Industrial-scale solar farms are directly integrated into the national grid through a layered technical pathway. Electrical output and operational data flow from inverters and PLCs through the local SCADA network, then to the plant control server or remote operations centre (ROC) via VPN or leased-line connections, and ultimately interface with the national grid control centre for generation reporting, dispatch control, and load balancing. However, in the absence of real-time cybersecurity visibility and active protection, malicious traffic, infected firmware, or unauthorised control commands originating within the solar farm can traverse this communication chain undetected.
Malicious Outcome: A compromised SCADA or engineering workstation can serve as a launch point for malware propagation toward grid supervisory systems. This can result in manipulated telemetry data, false generation values, or direct interference with grid interface controllers. In extreme cases, coordinated attacks may cause inverter shutdowns, transformer overloads, or cascading grid instability, extending the impact well beyond the originating site.
First Watch Solution: First Watch provides continuous detection and blocking across this end-to-end pathway — from the solar farm's field devices to its external grid connections. Using deep-packet inspection, protocol anomaly detection, and behavioural analytics, it identifies and halts malicious payloads, abnormal command traffic, and unauthorised data exchanges before they cross network boundaries. The platform automatically isolates compromised segments and blocks outbound malicious communication, preventing any infection or control manipulation from reaching the national grid control centre.
Why Active Protection Instead of Monitoring
Traditional monitoring solutions rely on detecting anomalies and alerting engineers, which creates several challenges:
- Requires a team of cybersecurity specialists to interpret alerts
- Generates high volumes of false positives, leading to alarm fatigue
- Often reacts too late, after malicious activity has already impacted operations
Recognising these limitations, the solar farm company chose Active Protection with First Watch. This approach stops malicious activity immediately instead of merely flagging it for later review.
Typical First Watch Platform Architecture
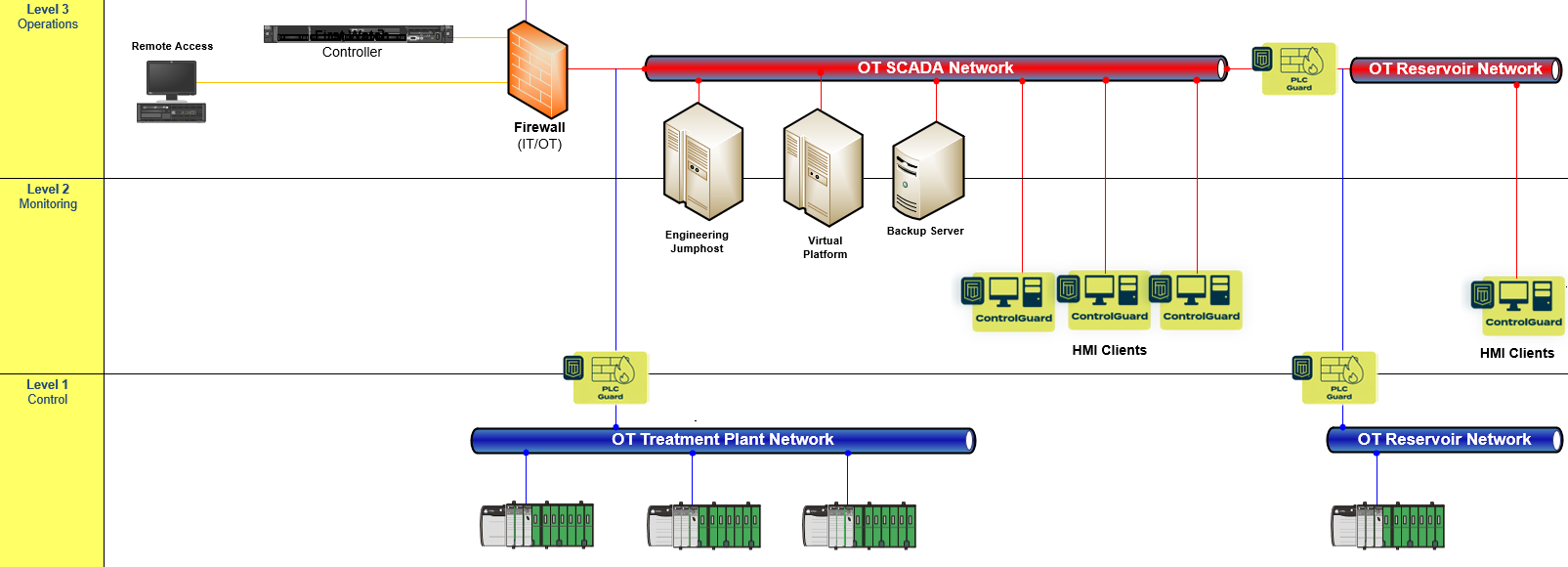
- Controller — central server collecting data and distributing rules
- ControlGuard — endpoint agent preventing unauthorised software on SCADA
- PLC Guard — network agent preventing unauthorised communication with PLC by Deep Packet Inspection (DPI)
How Active Protection Works for SCADA Computers and PLCs
First Watch deploys rule-based protection directly into the control environment:
- SCADA Computers — First Watch blocks unauthorised software execution, prevents malware from gaining persistence, and ensures only approved applications run
- PLCs — active protection enforces strict control logic integrity. Any attempt to modify PLC programs or issue unauthorised commands is automatically blocked
- Network Communications — rules ensure only valid commands and expected data flows between devices. Suspicious or out-of-sequence traffic is stopped at once
Unlike machine learning or anomaly-based tools, First Watch's deterministic, rule-based engine eliminates false positives by only enforcing what is explicitly allowed. This makes protection transparent to operators while ensuring maximum reliability.
What We Monitor — Solar Farm Specifics
Solar farms typically rely on Schneider Electric PLCs and Modbus protocol for communication between SCADA systems, inverters, and field devices. First Watch provides deep visibility and protection at the protocol level, going beyond generic network monitoring to understand the specific operations that matter in a solar farm environment.
Modbus Register Monitoring
PLC Guard performs deep packet inspection of Modbus traffic to detect and control operations at the register level:
- Setpoint write operations — detecting changes to power output setpoints, reactive power targets, and frequency regulation parameters
- Variable read/write monitoring — tracking all register read and write operations to identify unexpected access patterns or unauthorised modifications
- Inverter control commands — monitoring commands that affect inverter operating modes, power curtailment, and grid connection states
- MPPT and panel configuration — visibility into changes to maximum power point tracking parameters and array configurations
Schneider Electric PLC Protection
For Schneider Electric controllers commonly deployed in solar farm environments, First Watch monitors and controls:
- Firmware updates — blocking unauthorised firmware modifications that could compromise controller behaviour
- Software download and upload — preventing unauthorised logic changes to PLCs that govern inverter sequencing, grid synchronisation, and safety interlocks
- Connection with elevated privileges — detecting and controlling engineering sessions that have the authority to modify PLC configuration
- Change of PLC mode — alarming on transitions between Run, Stop, and Program modes that occur outside approved maintenance windows
- Configuration changes — tracking modifications to communication settings, I/O mappings, and module configurations
Process-Specific Visibility
Beyond protocol-level monitoring, the platform provides operational context specific to solar farm processes:
- Grid synchronisation parameters — monitoring changes to frequency, voltage, and power factor setpoints that govern grid interface behaviour
- Safety interlock states — tracking the status of protection relays, anti-islanding functions, and emergency shutdown sequences
- Inverter operating profiles — detecting deviations from approved operating envelopes that could indicate tampering or misconfiguration
This industry-specific depth ensures that First Watch doesn't just see network traffic — it understands the operational meaning of every communication and can distinguish legitimate solar farm operations from unauthorised or malicious activity.
Benefits
For the Solar Farm
- Reduced operational and cybersecurity risk, supporting compliance with critical infrastructure regulations
- No need for large cybersecurity teams to interpret or manage complex alerts
- Continuous real-time protection without disrupting energy production or maintenance workflows
For the Public
- Assurance of stable, uninterrupted power supply from renewable energy sources
- Strengthened resilience against cyberattacks that could affect grid reliability or national energy security
One of the key advantages is that Active Protection operates autonomously — it requires no continuous human supervision or manual intervention. The system automatically detects and blocks all malicious activity, ensuring that the solar farm remains secure, stable, and reliable as part of the national power grid.
For more information or to discuss a deployment for your solar farm, please contact us.