Cybersecurity for Timber Processing
Network Separation, Remote Access Control, and Active Protection

Background
Timber processing plants operate highly automated production environments where sawmill lines, drying kilns, grading systems, and packaging equipment are governed by PLCs and HMI workstations. These facilities face a unique combination of cybersecurity challenges that are often underestimated.
A critical characteristic of timber processing is that production machinery is frequently manufactured and maintained by overseas vendors. These machines require regular remote access for diagnostics, firmware updates, calibration, and troubleshooting — often connecting directly into the OT network from international locations. Without proper controls, these remote sessions represent a significant and persistent attack surface.
At the same time, timber processing plants typically operate with flat or poorly segmented networks where business IT systems and production OT systems share the same infrastructure. This means that a compromise on the corporate network — through phishing, ransomware, or a supply chain attack — can directly reach production controllers and HMI workstations.
Customer Profile
- Timber processing and manufacturing plant with multiple production lines
- HMI workstations controlling sawmill, drying, and grading equipment
- PLCs managing production machinery, many supplied by overseas vendors
- Remote maintenance access required by international equipment suppliers
- No dedicated on-site cybersecurity team
- IT and OT networks insufficiently separated
The Challenge
A comprehensive cybersecurity assessment identified critical vulnerabilities across the plant's OT environment:
- No separation between IT and OT networks — business computers and production systems shared the same network infrastructure, allowing threats to move freely between environments
- Uncontrolled remote access — overseas machine vendors connected directly to production PLCs and HMIs for maintenance, with no filtering or monitoring of what commands were being sent
- Legacy operating systems — production HMIs running older Windows versions with known vulnerabilities and no ability to upgrade due to vendor dependencies
- No real-time visibility — plant management had no awareness of what was happening on the OT network, who was connecting, or what changes were being made
- Periodic audits were insufficient — security assessments performed infrequently left long exposure windows between reviews
The Solution — PLC Guard as a Separation Device
The cornerstone of this deployment is the use of PLC Guard as a network separation and filtering device between the business (IT) network and the production (OT) network. Unlike a traditional firewall that operates at the IP and port level, PLC Guard provides deep packet inspection of industrial protocols, understanding the operational meaning of every communication passing between networks.
Network Separation
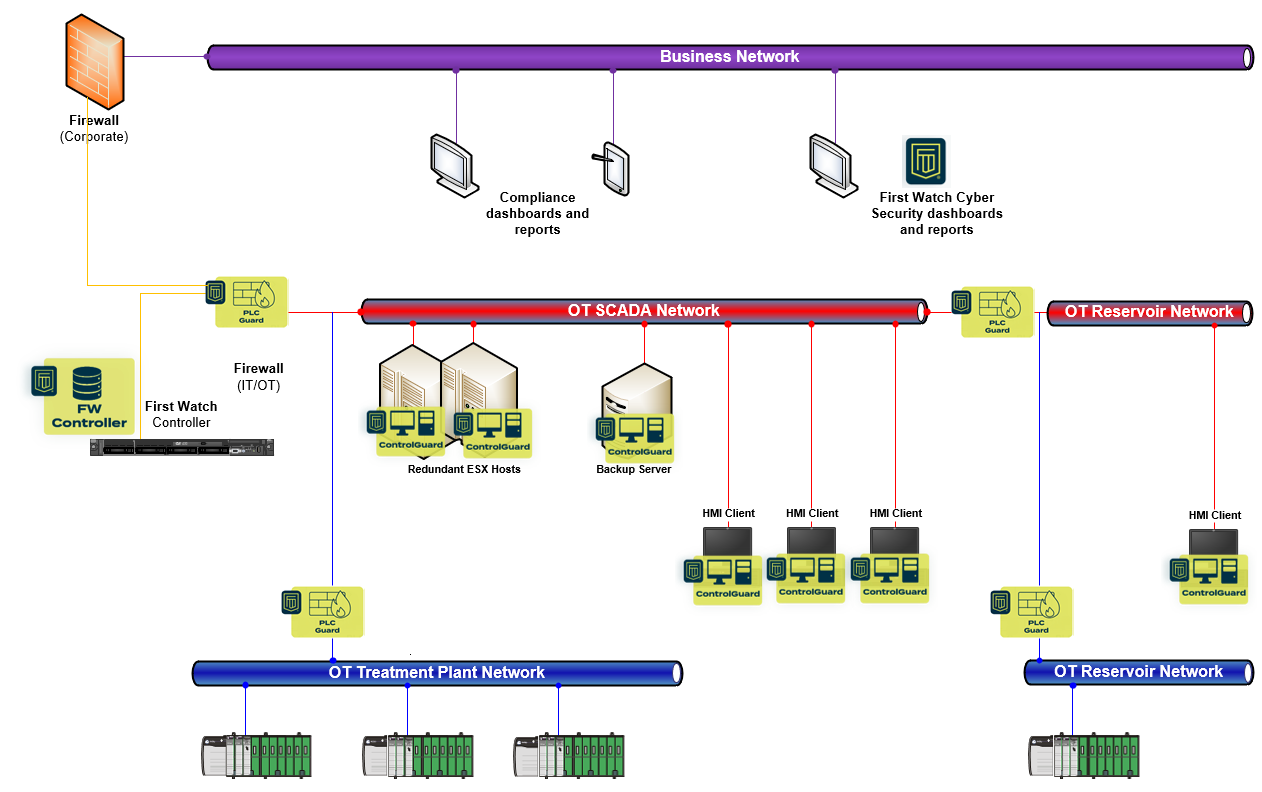
PLC Guard is installed inline between the IT and OT environments, creating a controlled boundary:
- All traffic between business and production networks passes through PLC Guard — no direct, unfiltered path exists between the two environments
- Only authorised communications are permitted — PLC Guard enforces policies that define exactly which hosts can communicate with production systems, over which protocols, and with what operations
- Unauthorised connection attempts are blocked and logged — any device or user attempting to reach production systems without authorisation is stopped at the boundary
This transforms PLC Guard from a simple monitoring tool into an active separation device that enforces network segmentation at the industrial protocol level.
Remote Vendor Access Control
For overseas machine vendors requiring remote maintenance access, PLC Guard provides granular control over what remote sessions can do:
- Vendor connections are filtered at the protocol level — remote sessions can be permitted to read process variables and diagnostics while being blocked from modifying PLC logic or firmware
- Programming operations require explicit authorisation — firmware updates, logic downloads, and configuration changes from remote vendors can only proceed when approved through the platform's governance process
- All remote activity is logged with full attribution — every command sent by a remote vendor is recorded with timestamps, source identification, and operation type
- Session-level visibility — plant personnel can see in real time what a remote vendor is doing on the production network
This ensures that overseas vendors can perform their required maintenance while the plant maintains full control and visibility over what actions are taken on production machinery.
ControlGuard — Endpoint Protection
ControlGuard agents are installed on all HMI workstations and Windows-based production systems:
- Application whitelisting — only approved software is permitted to execute, protecting legacy Windows machines that cannot be patched or upgraded
- Malware prevention — ransomware, trojans, and other malicious software are blocked before execution, regardless of how they are delivered
- Monitoring of critical events — privilege escalations, PowerShell sessions, unauthorised software installations, and configuration changes are detected and alarmed
This is particularly critical for legacy Windows 7 machines that remain in production due to vendor dependencies and cannot receive security patches.
Visibility and Monitoring
Beyond active protection, the deployment provides comprehensive operational visibility:
Real-Time Network Visibility
- Complete inventory of all devices communicating on the OT network — including devices that were previously unknown
- Communication flow mapping — visibility into which devices are talking to each other, over which protocols, and how frequently
- Anomaly detection — identification of unexpected communication patterns, new devices, or unusual traffic volumes
Continuous Monitoring
- 24/7 automated monitoring — the platform continuously monitors the OT environment without requiring on-site cybersecurity staff
- Alarm generation — security events trigger alarms that are escalated to responsible personnel
- Monthly SOC reporting — structured reports covering asset state, software inventory, network connections, anomalous events, and changes to devices or behaviour
Change Detection
- Hardware and software changes are detected automatically across all protected assets
- New devices appearing on the network are identified and flagged for verification
- Configuration modifications to PLCs and HMIs are tracked with full provenance
What We Monitor — Timber Processing Specifics
Timber processing plants rely on specialised machinery with vendor-specific control systems. First Watch provides visibility into the operations that matter in this environment:
- Sawmill line controllers — monitoring PLC operations that govern feed rates, blade positioning, and log scanning systems
- Kiln drying controllers — visibility into temperature, humidity, and airflow setpoints that affect timber quality
- Grading and sorting systems — tracking configuration changes to automated grading parameters
- Vendor remote sessions — complete logging of all remote maintenance activity, including commands sent, parameters changed, and firmware operations
- VPN and remote access connections — monitoring all inbound remote connections to the OT environment with source identification and session duration
Benefits
For the Plant
- Network separation without infrastructure overhaul — PLC Guard provides IT/OT segmentation at the protocol level without requiring complete network redesign
- Controlled remote vendor access — overseas machine suppliers can maintain equipment while the plant retains full visibility and control
- Legacy system protection — Windows 7 and other unsupported systems are protected through application whitelisting regardless of patch status
- No dedicated cybersecurity team required — protection is autonomous and continuous
- Monthly SOC reporting — documented evidence of cybersecurity posture for governance and compliance
For Production
- Zero disruption to manufacturing operations — protection is transparent to production processes
- Vendor maintenance continues uninterrupted — approved remote sessions proceed normally; only unauthorised actions are blocked
- Visibility for plant management — real-time awareness of who is accessing production systems and what they are doing
The deployment demonstrates that PLC Guard as a network separation device provides manufacturing plants with a practical, effective way to segment IT and OT environments while maintaining controlled access for remote vendors. Combined with ControlGuard endpoint protection and continuous monitoring, the plant achieves comprehensive cybersecurity coverage without requiring specialist on-site staff.
For more information or to discuss a deployment for your manufacturing facility, please contact us.