Mid Size Deployment
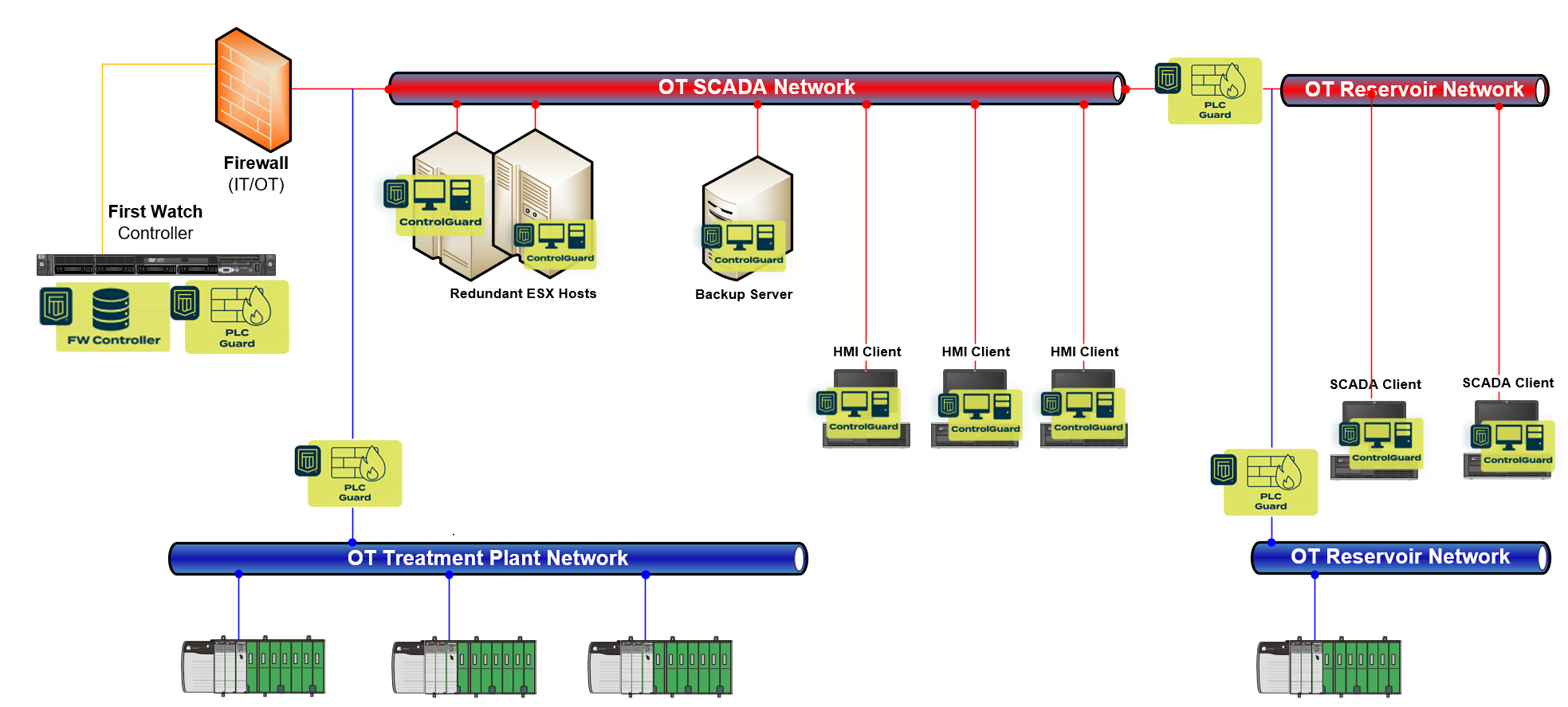
The mid size deployment model is designed for industrial environments with multiple production facilities, each responsible for a specific product or intermediate process step. This model supports 1 Controller, multiple PLC Guards, and multiple ControlGuards scaled to the number of endpoints across the plant.
In practice, a mid size deployment is a combination of multiple small size scenarios, unified under a single Controller for centralised visibility, alarm management, and policy governance.
Hybrid Deployment Model
The defining characteristic of the mid size deployment is its hybrid approach — different areas of the plant operate under different protection levels simultaneously. This reflects the operational reality that not all assets carry the same risk, and not all areas are at the same stage of deployment maturity.
In a typical mid size deployment:
- Multiple PLC Guards are deployed across the plant — some operating in monitoring mode and others in enforcement mode, depending on the criticality and readiness of each area
- All Windows computers are protected with ControlGuards — providing consistent endpoint visibility and protection across SCADA clients, engineering workstations, and servers
- Each production facility or process area is treated as a distinct protection zone, with its own policies and enforcement posture
This hybrid model allows organisations to progressively extend enforcement across the plant — starting with the most critical areas and expanding as operational confidence grows.
Balancing Enforcement and Monitoring
The main challenge in a mid size deployment is finding the correct balance between enforcement and monitoring. This balance is driven by asset criticality, operational risk, and deployment maturity.
As a general rule:
- All critical assets must be protected — controllers, safety systems, and key production infrastructure operate under active enforcement policies
- Remaining assets must be monitored — less critical systems benefit from visibility and alarm capabilities while enforcement policies are developed and validated
This approach ensures that the highest-risk areas receive deterministic protection first, while the rest of the environment is never left unobserved.
Addressing Blind Spots
In complex network topologies, there will always be areas that are difficult to protect and expensive to monitor. These blind spots — network segments, legacy devices, or isolated subsystems — represent potential vectors from which attacks can be initiated.
Acknowledging blind spots is an essential part of the deployment design process. The mid size model addresses this by:
- Mapping the full network topology during the solution design phase to identify areas of limited visibility
- Prioritising protection investments where the operational and security impact is greatest
- Using monitoring as a compensating control where inline enforcement is not practical or cost-effective
- Documenting known gaps so they can be addressed through infrastructure changes, segmentation improvements, or future deployment phases
The goal is not to eliminate every blind spot immediately, but to ensure that they are known, documented, and managed within the organisation's governance framework.
Operational Characteristics
| Aspect | Mid Size Deployment |
|---|---|
| Controller | 1 (centralised) |
| PLC Guards | Multiple — hybrid monitoring and enforcement |
| ControlGuards | All Windows endpoints protected |
| Deployment approach | Combination of multiple small size scenarios |
| Protection strategy | Critical assets enforced, remaining assets monitored |
| Key challenge | Balancing enforcement, monitoring, and blind spot management |
The mid size deployment model provides the flexibility to protect complex, multi-facility industrial environments while acknowledging the operational realities of varied criticality, network complexity, and progressive deployment. By combining enforcement where it matters most with monitoring across the broader environment, organisations achieve comprehensive visibility with targeted protection — managed centrally through a single Controller.